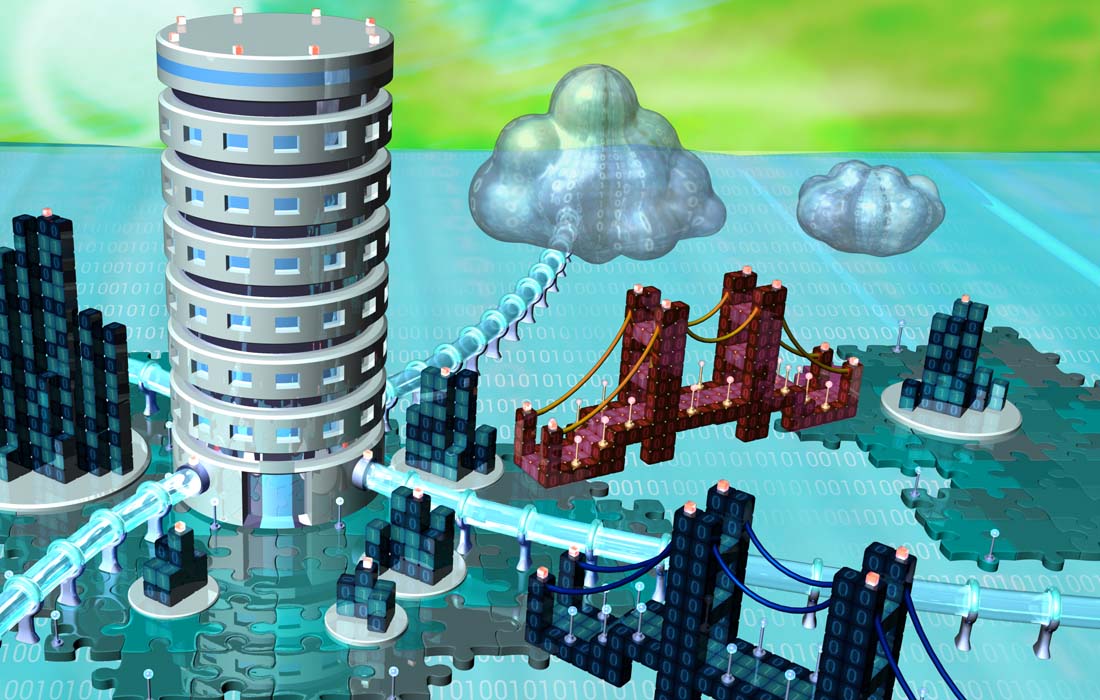
Cyber Simulation Suite is a visualization and modeling platform for executive level Cyber Security topology and policy
You have a talented and well-funded IT department using best practices. Despite your team’s efforts, you are woken in the night by phone. Your organization has been hacked. What do you do?
Explore strategic options surrounding threats to your organization.
The platform models the relationships between security topology, policy, economy, and service satisfaction, allowing users to experiment with the trade-offs and double downs of planning and decision making at the CISO level.
With the support of IBM’s System Z and Security leadership, Hazardous Software has developed a validated simulation platform of top level systems for large organizations. By stress testing topologies and policy approaches in a simulated environment of heightened risk, users can identify and optimize against key strategic vulnerabilities, reducing risks to the organization.
Iterate to Maximize
Integrity
Availability
Resiliency
Graceful degredation
Accommodate
Performance
Costs
Regulations
Physical attack surface
Cyber attack surface
Stress-test Policy
Reduce rate of successful external attacks
Improve communication with customers
Reduce fallout from compromised systems
Reduce compromises from physical and insider threats
Leverage your own data and campaigns
Corporate strategy optimization
Organizational modeling
Cyber ranges
Marketing
Communication
Training
Build a bridge between staff and AI
As a serious game environment, Cyber Simulation Suite marries game theory to decision support and places it squarely in your hands. Simulate your own business environments, including customer models, corporate landscape, topology, and scenarios. Substitute your own data as needed. Pound your system with simulated cyber attacks to see how long it lasts and where it breaks down.
Let us provide the rules that complete the picture, and leverage a training bed that makes your team stronger.
For questions or further info, please contact us at info@www.hazardoussoftware.com